Because “set it and forget it” shouldn’t be a strategy
Security and compliance teams need to know exactly what sensitive data is flowing through their environments and where it’s going. Because surprise PII is no one’s favorite kind of surprise.
Meanwhile, upstream teams are shipping new apps, changing schemas, adding fields, and generally moving fast.
However, you can only manage and protect the data you currently know of and expect.
But sensitive data has a habit of showing up where no one expected it…
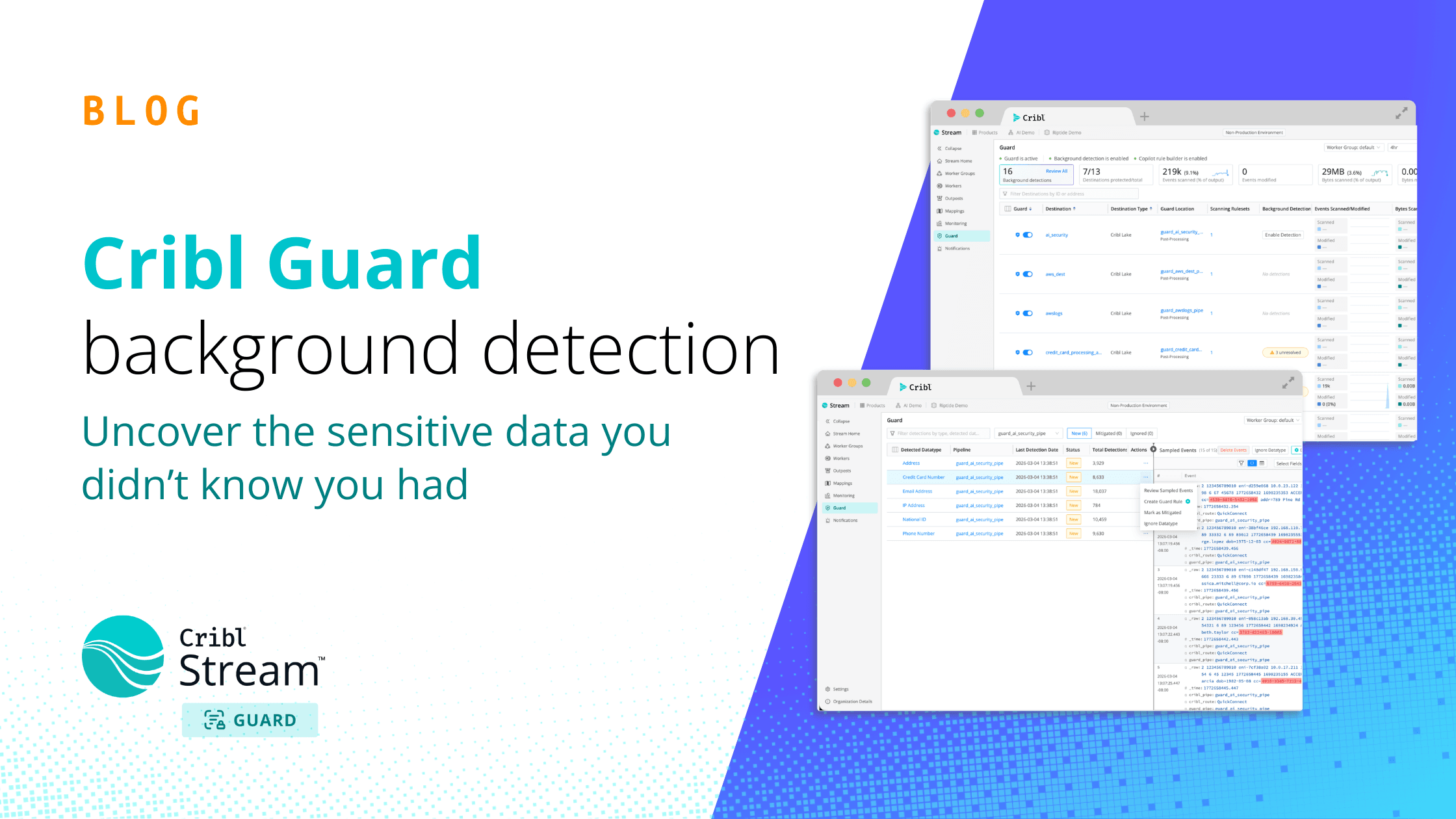
That’s why in Cribl Stream 4.17, we’re introducing background detection, an AI-powered capability in Cribl Guard that uses a custom-built AI model designed specifically for telemetry data to continuously analyze data flowing through Pipelines to uncover previously unknown sensitive data before it causes an issue.
The real problem: Unknown unknowns
Most organizations rely on predefined data processing rules to catch known patterns of PII, secrets, or regulated data. That can work for a short period but only until something inevitably changes.
Security and platform teams face:
Lack of visibility into unknown risk: rules only detect what has already been anticipated.
Constant schema changes: new fields and formats are introduced without always notifying security teams.
Increasing compliance pressure: it is no longer enough to configure rules once. Organizations must demonstrate ongoing monitoring and mitigation.
Risk amplification downstream: if sensitive data reaches a SIEM, data lake, or observability platform, exposure spreads quickly.
Manual review that does not scale: no team can realistically inspect every data change across pipelines on a frequent basis.
What’s needed isn’t just enforcement but continuous discovery.
So what is background detection?
Background detection is an AI-powered capability in Cribl Guard that continuously analyzes data flowing through Pipelines to uncover sensitive information that may have gone unnoticed.
Instead of relying solely on static rules, background detection uses custom transformer-based AI models developed by the Cribl team and trained specifically for telemetry and machine data environments to identify new and emerging patterns of PII, regulated data, secrets, and other sensitive content.
As upstream systems evolve, background detection monitors for drift in the background. It flags new risk as it appears, not six months later during an audit.
When new sensitive data is identified, it’s surfaced in a centralized interface. You can review the detection, inspect sampled events, dismiss it, or immediately create or refine Guard rules to stop future matches from reaching downstream systems.
In other words, it enables organizations to move from static policy enforcement to continuous, AI-driven risk discovery and mitigation, helping reduce the financial and operational impact of unexpected sensitive data exposure (and making sure the "well that’s new" moments stay out of incident reports.)
What this means for you
You uncover hidden risk before it becomes an issue. Instead of discovering sensitive data after it’s already landed in your analytics stack, you catch it in flight. And that means fewer late nights for you cleaning up preventable messes!
You shorten the path from detection to protection. Quickly convert findings into Guard rules before exposure spreads.
You stay ahead of schema drift. As new applications and fields appear, background detection’s AI helps flag patterns that deserve a look.
You reduce regulatory and operational risk. Preventing unintended sensitive data from reaching high-risk systems lowers the likelihood of audit fines, breach notifications, and expensive remediation efforts.
You strengthen audit readiness. You can demonstrate continuous monitoring and documented mitigation instead of pointing to rulesets that haven't been revisited in a year.
How teams are using it
Prove and improve your data risk posture
Security teams use background detection to surface what was previously invisible and impossible for overworked teams to discover while reducing exposure, not just relying on a static ruleset.
Protect high-value destinations
Compliance and observability teams apply background detection to critical destinations such as SIEMs, data lakes, observability platforms, and ticketing systems. If new sensitive data is detected flowing to one of these systems, teams can immediately update Guard rules or adjust routing to stop the issue before it turns into a bigger, messier problem. Any data that has already reached the destination can be replayed and removed with Cribl Stream.
Monitor schema changes and data drift
Stream operators treat background detection as an early warning system for upstream sensitive data changes. When new fields appear, AI flags them so Guard rules can be refined without guesswork or fire drills.
Support reporting and audits
Risk and audit teams use findings to clearly document what was detected, what action was taken, and when it was mitigated which creates defensible evidence of continuous monitoring instead of scrambling for answers later.
Behind the scenes: Training AI for telemetry
While detecting PII isn’t new, doing it effectively with telemetry data is a unique challenge. Background detection had to meet a few key requirements: keep up with high-throughput environments, make sense of semi-structured log data, work out-of -the-box with little to no user input, and run directly in customer environments.
Most off-the-shelf models and rule-based approaches just aren’t built for that. So we built our own.
We started with a pre-trained BERT (Bidirectional Encoder Representations from Transformers) model and fine-tuned it specifically for telemetry data. That meant generating large synthetic datasets (with the help of Cribl Packs) with hundreds of thousands of labeled log events so the model could learn how sensitive data actually shows up in real-world machine data.
The result is a model that’s both fast and efficient. It’s much smaller than traditional LLMs and optimized for high-speed detection. And because it uses an encoder-only architecture, it can analyze data quickly without the lag you’d typically expect from generative models.
Just as importantly, it runs directly on the worker node so your data stays in your environment to help meet any compliance or security requirements.
In short, this isn’t just AI applied to telemetry but rather it’s AI built specifically for it.
Getting started
To start using background detection, upgrade to Cribl 4.17 and ensure you have an Enterprise license.
1. Enable background detection
Ensure Cribl Guard is enabled for at least one Destination.
Turn on background detection in AI Settings.
Enable it for specific Worker Groups, Destinations, or Pipelines.
Optionally refine scope within individual Guard Functions.
Commit and deploy your changes.
You control exactly where and how this AI-powered capability is applied.
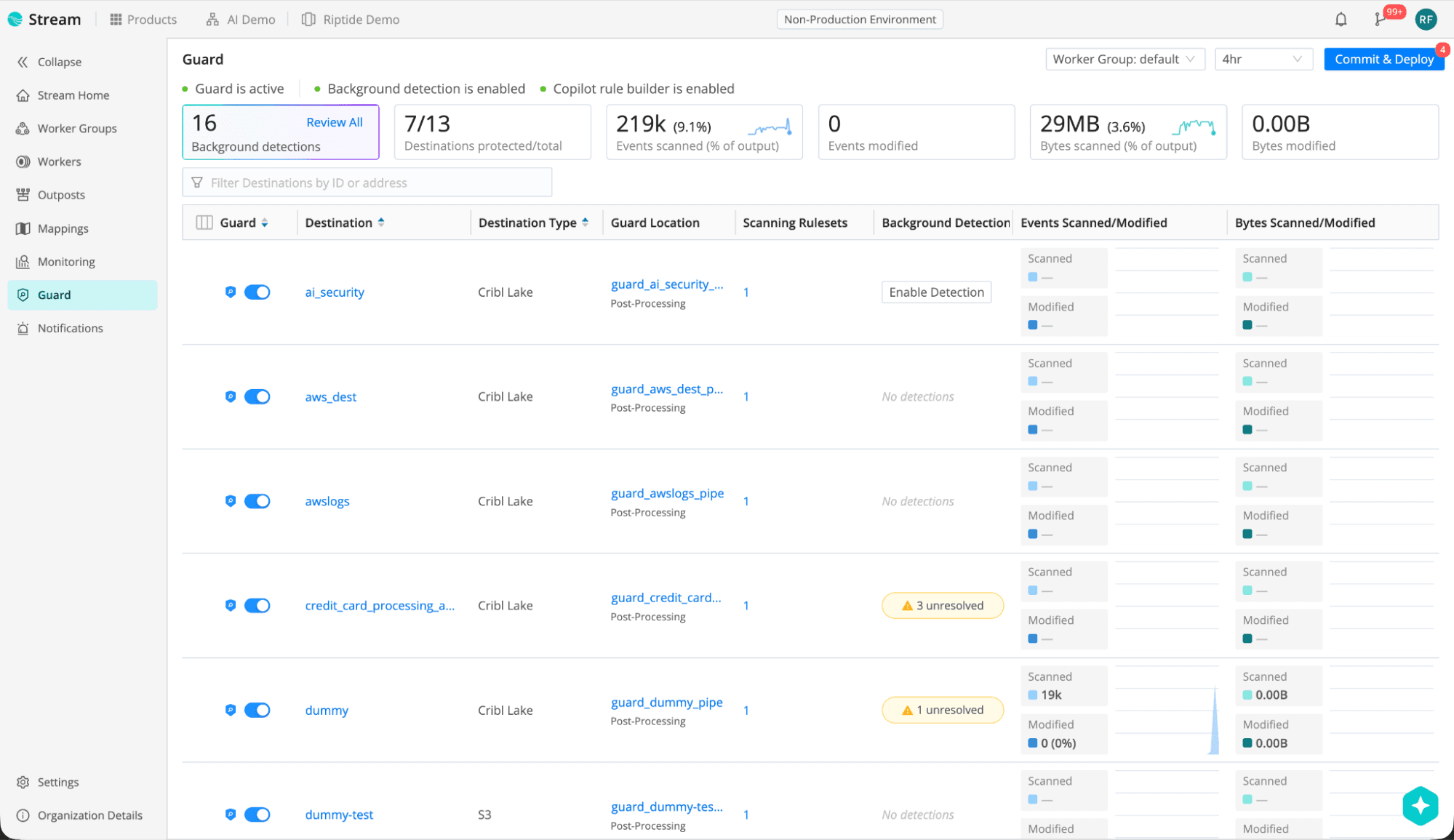
2. Review detections
From the Guard homepage, select Review All in the background detections tile, or click the yellow detections alert in the background detection column for a specific Pipeline.
Then select a detection type (such as CREDIT_CARD_NUMBER) to view sampled events and understand the scope and context of the finding.

3. Mitigate and take action
From the Actions column, you can:
Create a Guard rule (using Copilot suggestions or manually) to mask, drop, or otherwise mitigate future matches, and then add the rule to a Scanning Ruleset (and commit and deploy) to enforce it going forward
Mark findings as Mitigated to document that the issue has been addressed
Ignore a datatype to suppress future detections of that type

The workflow is simple: detect, review, mitigate. For additional details, refer to Cribl’s documentation.
From static policy to continuous discovery
In modern data environments, schemas don’t stay static. They change constantly and usually without telling you.
Background detection in Cribl Guard ensures your sensitive data protection constantly keeps up, instead of leaving you to hope for the best until the next time you manually check up on it.
AI-driven discovery with integrated mitigation workflows lets you move beyond one-time rule configuration and into continuous risk identification and control before those “minor changes” turn into fire drill meetings, compliance escalations, or emergency Slack channels.
Under the hood, background detection is powered by custom AI models developed by the Cribl team specifically for telemetry. It’s part of our broader effort to bring purpose-built AI into IT and security environments, and we’re continuing to invest heavily in developing new AI-driven capabilities.
Start scanning with Cribl Guard background detection today on Cribl 4.17.