I’ve been an investigator, an engineer, an analyst, and an architect, but at heart I am a systems integrator. So it’s no surprise I believe that you use the best system available for each task, and then you intelligently orchestrate your systems leveraging purposeful integrations everywhere possible. Instead of buying a platform and bending your environment to its limits, what if you could engineer your own detection and response ecosystem?
The challenges of modern detection and response demands that defenders rethink the model. To design a composable SIEM architecture built for interoperability, automation, and evolution is not about abandoning the SIEM; it's about evolving it into a framework that’s built to keep pace with the complexity, scale, and speed of threats, as well as the proliferation of artificial intelligence (AI). This shift is happening, from a monolithic SIEM platform approach, to one that delivers the agility, precision, and automation required for what’s next.
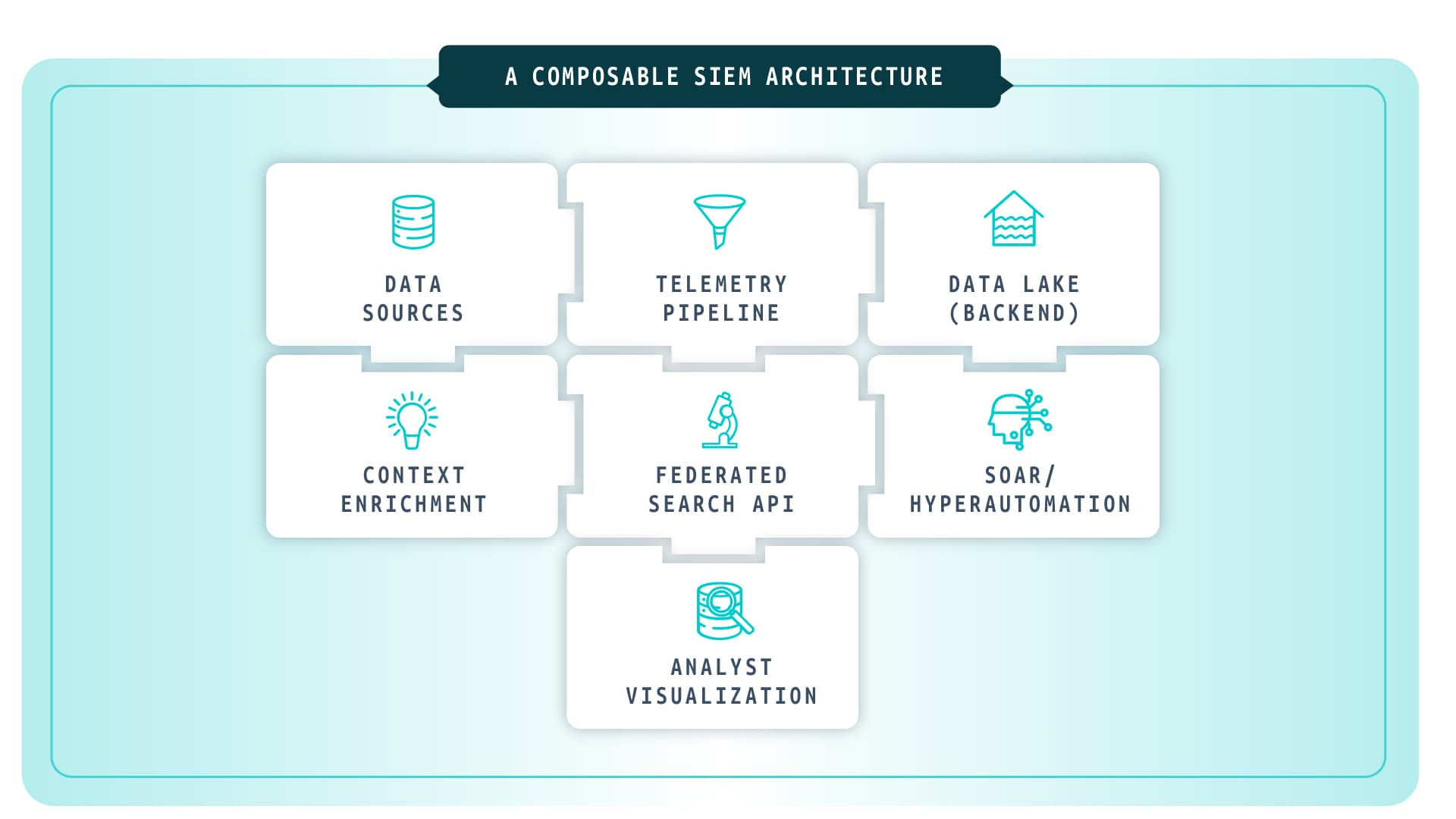
The Composable SIEM Stack
I’ve spent much of my career exploring how security data moves, from collection and normalization to detection and response. Along the way, I’ve built SIEM stacks from scratch and have also had the privilege of helping organizations rethink their SIEM architectures to be more open, scalable, efficient, and adaptive. In most cases the organization either has to grow into the SIEM they are implementing or is too large for a single SIEM to be the entire brains of the operation. Through the years I’ve learned that there is no perfect SIEM for any one organization, you get what you put in.
A composable SIEM doesn’t eliminate the SIEM, it deconstructs it and implements the components that are most critical to the extent that the organization needs or can afford to. Each layer of the security detection and response workflow becomes its own function, each with a preferred platform and its own level of automation. This flexibility can allow an organization to fully automate some components of their security workflow while limiting the automation in other aspects of the operation based on their confidence level in each corresponding system.
Every SOC Leader Knows This Tradeoff
Platformization promises simplicity: one vendor, one contract, one pane of glass. But it often sacrifices agility and innovation.
Best-of-breed offers specialization: pick the right tool for each job. Yet it requires integration effort and architectural discipline.
A composable SIEM empowers you to embrace both choice and control. You can have the flexibility of best-of-breed tools, while maintaining a unified control plane through pipelines, APIs, and orchestration layers. The real standard isn’t which vendor you choose; it’s your commitment to interoperability. Once that foundation is set, your architecture becomes future-proof. You can add or swap technologies without disrupting workflows or losing data fidelity.
Building a Detection and Response Ecosystem
Before you can build a detection and response ecosystem, you need a clear security strategy to anchor it. The architecture only works when it’s shaped by your non-negotiables: what you must protect, the risks you refuse to accept, and the realities of your time, scope, and resources. These strategic guardrails determine which data matters most, where automation brings the highest return, and how each layer of the ecosystem should operate. With that foundation in place, the components that follow move from a list of capabilities to a deliberate, coherent system built to support how your organization detects, reasons, and responds.
Data Sources: Everything starts with data.
Endpoints, network devices, identity systems, SaaS platforms, and cloud infrastructure all generate critical telemetry and security context. The goal is total observability across all environments.
Data Pipeline / Normalization: The pipeline is where chaos becomes structured.1
Control of your data pipeline allows teams to filter, transform, mask, and enrich data before it ever hits storage, reducing noise and cost while preserving context.
Context Enrichment / Identities, Assets, TI: Enrichment connects signals to meaning.
Linking user identities, asset inventories, and business systems. This is where detections shift from “something happened” to “something important happened”.
Data Lake / Performant Backend: Separate compute from storage.2
A composable SIEM leans on open data lakes and data tiering for scalability and cost control, allowing analysts to query vast datasets without vendor lock-in.
Detection-as-Code / Detection Engineering: This is where security meets DevOps. 3
Detections are written, versioned, and tested like software enabling continuous improvement, better collaboration, and reproducibility across environments.
Agentic AI / Hyperautomation: Response automation becomes the next evolution.4
Instead of pre-scripted playbooks, AI-driven SOAR platforms enable dynamic orchestration, responding intelligently based on risk, confidence, and context.
Visualization / Investigations: Dashboarding and reporting become team-specific.
Analysts, engineers, and executives each get tailored dynamic insights, decoupled from the monolithic SIEM interface.
Federated Search / API Query: The dream state is to query once, search everywhere.
An API-first model allows analysts (and AI agents) to pivot across data sources and tools without friction.
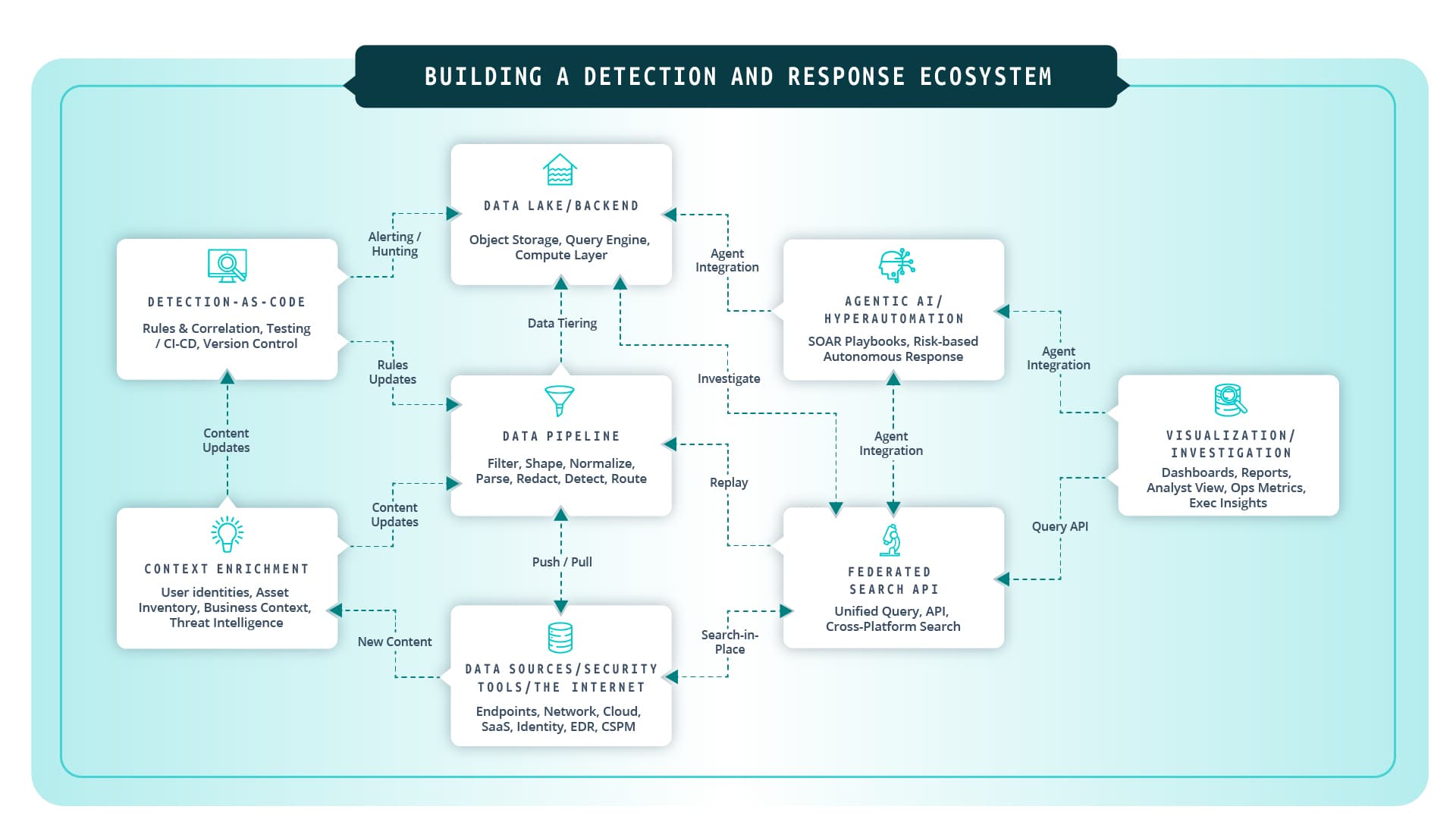
Each of these layers can be automated to different degrees, forming the backbone of autonomous security operations. As organizations mature, they progressively move from manual operation to agentic orchestration, one where systems communicate, learn, and act on their own. To deliver the context needed for detection and response at AI speeds and during retrohunts every system needs to be available to every other security system with proper guardrails and thoughtful integration points.
Engineering Toward Autonomy
Agentic AI systems are already reshaping how SOCs operate. They are reading machine generated log data while searching and augmenting their reasoning with human generated text from ticketing systems, knowledge bases, and collaboration tools. Leveraging both machine and human generated data to make informed decisions on remediation or mitigating actions is where security operations are headed. Imagine large language models and specialized agents that:
Analyze alerts and prioritize based on business impact.
Identify novel threats without pre-defined logic around specific detections.
Tune detection logic dynamically based on false-positive patterns.
Trigger orchestrated responses across your stack, without waiting for human input.
Perform root cause analysis based on existing telemetry and system behavior.
AI becomes the orchestrator of orchestrators, governing your collection, detection, enrichment, analysis, and response layers. The SOC of the future is not about human-designed playbooks and monolithic SIEM platforms with all-encompassing security capabilities. It’s more about AI-directed workflows, where analysts supervise, refine, and steer strategy while automation handles the mechanics of detection and response via API-first agentic workflows. A composable SIEM is what makes that autonomy possible.
When every component exposes an API and supports event-driven automation, AI can act as the connective tissue, turning your SOC into a living system that learns, adapts, and scales. Whether you’re normalizing logs before storage, enriching detections with identity data, or feeding telemetry into AI models for autonomous decision-making, at the foundation of this entire shift lies data control.
The Case for Composability in SIEM
For years, the industry has treated the SIEM as the “brain” of the SOC, an all-knowing system meant to collect, correlate, and respond. But reality has shown that as environments grow more complex, monolithic SIEMs struggle to keep pace. Their rigid architectures often force security teams to conform to vendor roadmaps rather than operational needs. The result is predictable: rising costs, slow iteration, and analytics pipelines that lag behind the threats they’re meant to detect.
As security operations evolve, so must the systems behind them. Cloud-native architectures, AI adoption, agentic workflows, the rise of SaaS, and the explosion of telemetry have outgrown the assumptions that drove early SIEM design. We now live in a world where new data sources appear daily, detections need to be tested like software, and automation has become the only way to scale.
A composable SIEM architecture embraces the idea that no single vendor can excel at everything. Instead of getting locked into an all-in-one suite, teams can build a modular stack of best-of-breed tools, each handling a specific function or multiple components, and orchestrate them through open APIs, pipelines, and shared data models. The value of this approach is simple: choice, flexibility, and control.
1. Noisy or unnormalized data impedes effective analysis: 46% of security and IT leaders admit that a lack of clean, high-quality data is undermining their security. Gigamon 2025 Survey
2. Data Lakes are becoming ubiquitous: the global data lake market is projected to reach US $20.1 billion by 2029, growing at a 20.6% CAGR from 2022 to 2029. Top 10 Future Trends in Enterprise Data Management, Scikiq
3. According to Gartner, by 2028, 75% of enterprise software engineers will use AI code assistants (up from less than 10% in early 2023). Gartner Press Release, April 2024
4. In 2024, organizations extensively using security AI and automation identified and contained breaches 100 days faster than those that didn’t. IBM Cost of a Data Breach Report 2024