
Use Cases
Logs, metrics, traces without the hassl.
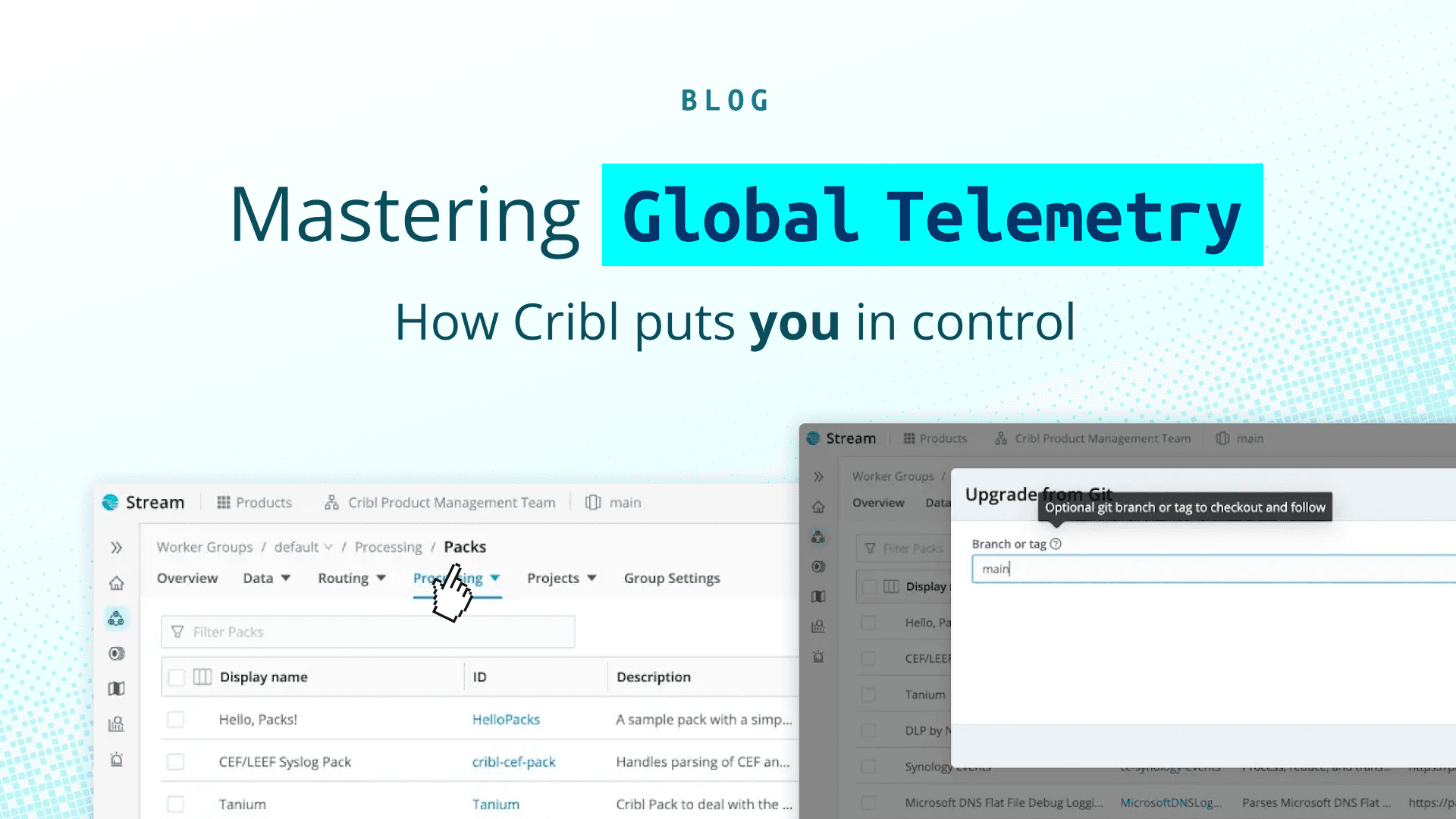
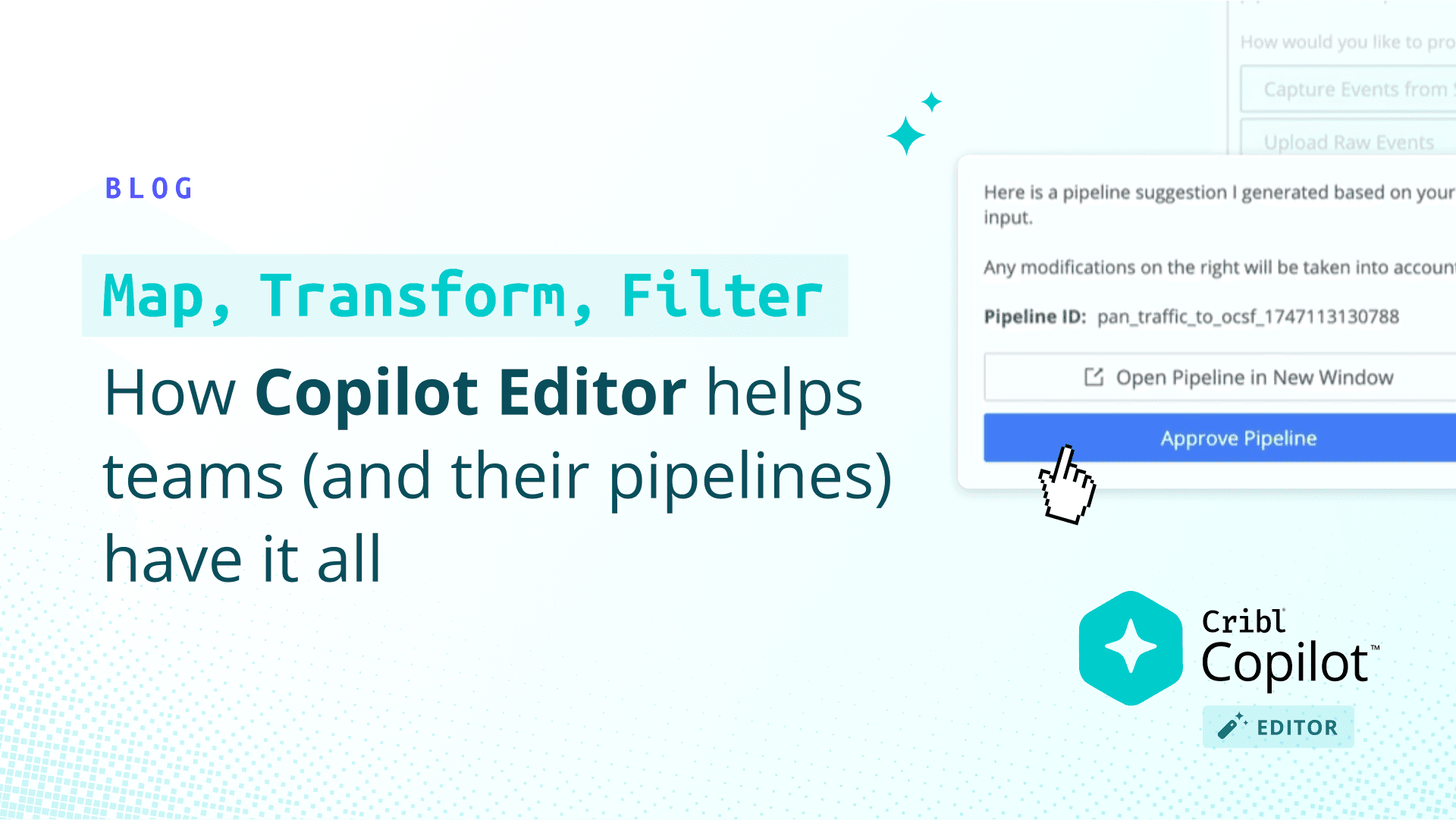
Simplify how you route, transform, and reduce data with a central tier that provides choice, flexibility and control.


Simplify how you route, transform, and reduce data with a central tier that provides choice, flexibility and control.


Integrations
The tools you love, made extra controllabl.
Shape and move data to any tool - no new agents or infrastructure. Choice, control, AND flexibility? Yes, please!
Customer Testimonials
CriblCon 25
Unite with the galaxy’s brightest minds for best practices, thoughtful insights, and innovations at CriblCon 25. Join this intergalactic gathering to see:
Cribl’s founders and executives unveil new product innovations
Live demos of cutting-edge solutions
Real use cases from industry leaders and peers

Good Reads



get started
See demos by use case, by yourself or with one of our team.
Get hands-on with a Sandbox or guided Cloud Trial.
Process up to 1TB/day, no license required.



