When working with sensitive data, there’s no skimping on security. Keeping data protected and private is paramount at Cribl, which is why we prioritized building a robust framework for Role-Based Access Control (RBAC), and with this latest release, we created an authorization system across the entire Cribl suite. WOOHOO!! 🥳
Cribl’s new authorization support enhances security by giving you control over who has permissions and privileges to access Cribl products, capabilities, and resources. This ensures users only see and access what they’re permitted to based on their assigned role. This level of authorization helps safeguard organizations against potential security threats.
After many conversations with some of our largest customers, we learned there are different requirements for different team members within an organization:
Admins are tasked with setting up Single sign-on (SSO), updating global settings, building worker groups, fleets and sub-fleets, and adding users with varying levels of permissions.
Editors are power users who do the day-to-day work of setting up new sources, destinations, tuning settings for optimal performance, and creating and managing datasets.
Users focus on working with data, creating pipelines, and working with datasets. Users don’t need to know the underlying infrastructure, they are there to work with the data.
And what our customers wanted was for Cribl to build a role-based authorization feature that could address these distinct needs, providing the necessary tools to enable team members to perform their specific roles effectively while maintaining the appropriate level of access. With future releases, we will continue expanding and refining our authorization privileges to meet the needs of organizations of all shapes and sizes. And of course, continue to fortify data security and empower our customers to work within a secure environment.
How It Works
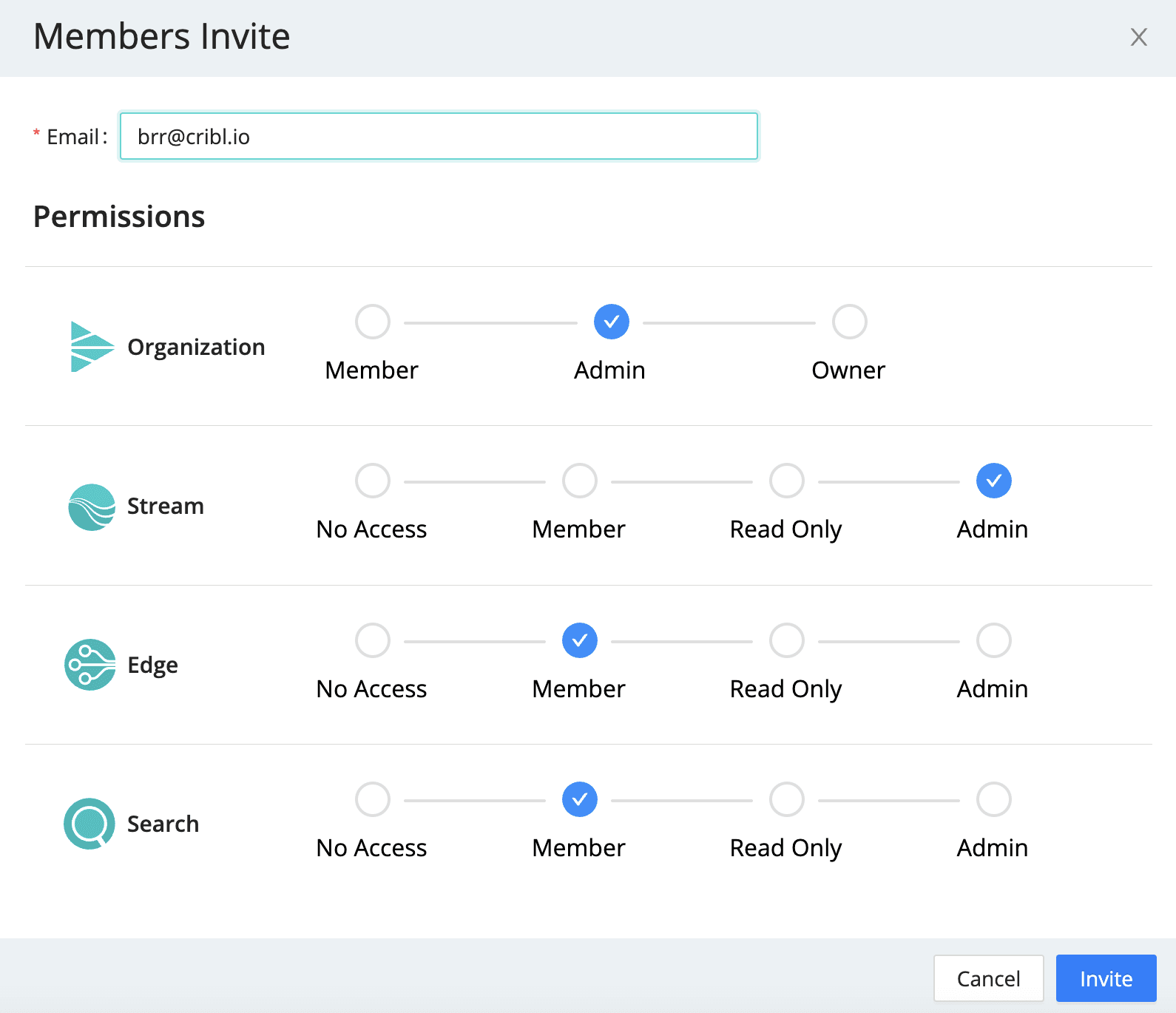
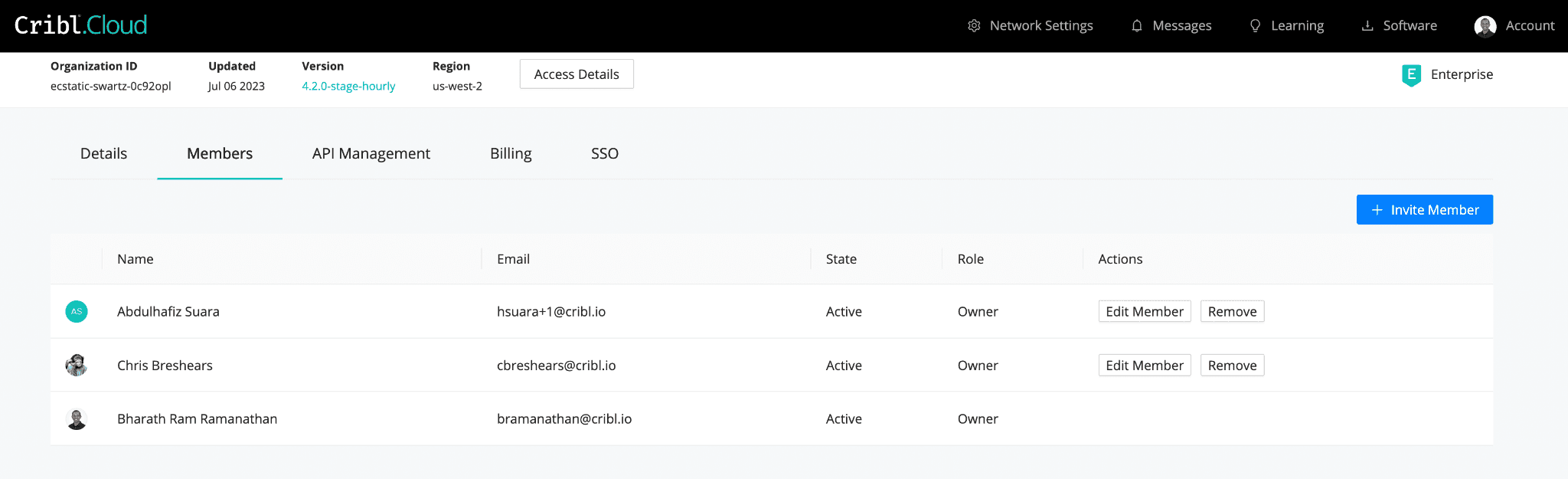
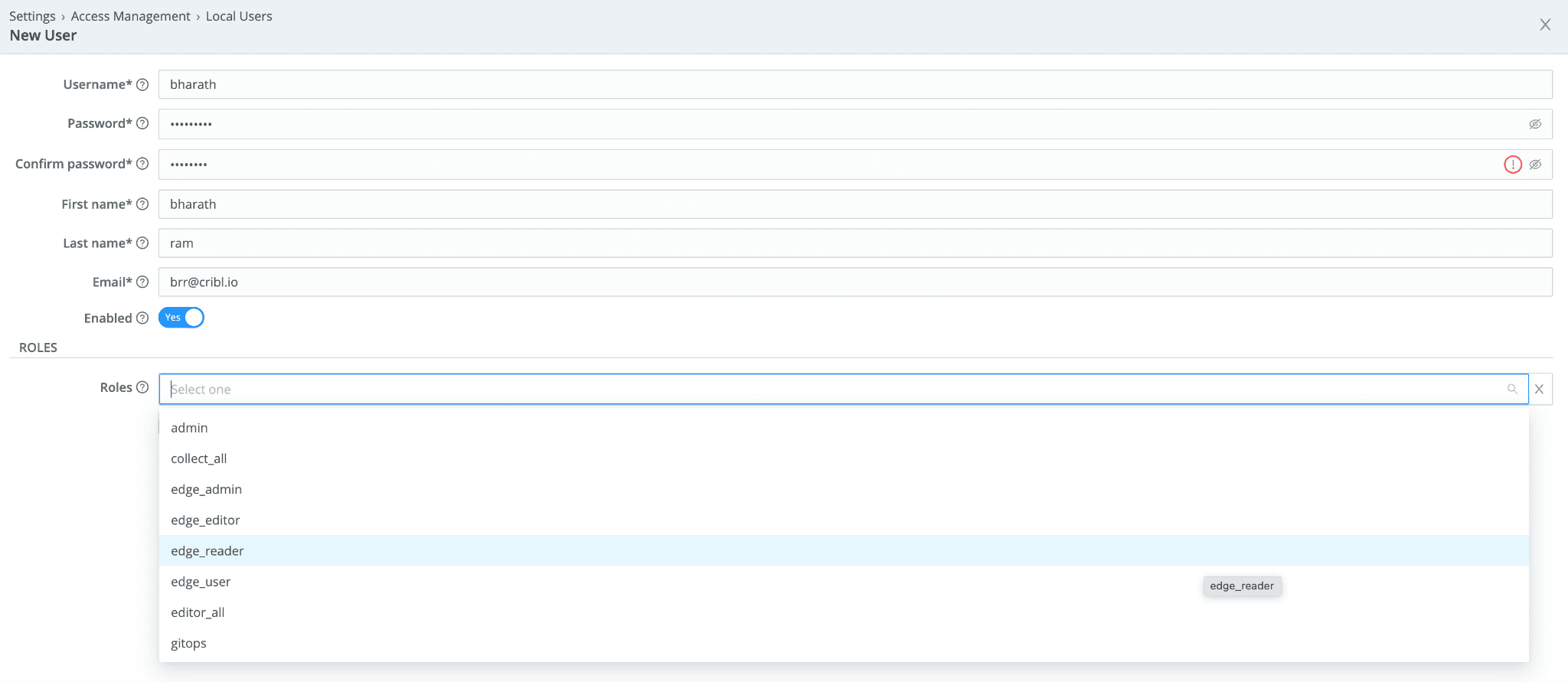
A new Organization Member management page allows for a unified experience across both cloud and on-prem environments for access management across all Cribl products. The privileges and capabilities offered include:
Inviting and managing new and existing members
Assigning members to one or more products
Setting product-level access for members
An example of how authorization can be configured:
Cribl’s new Members authorization tools work with your IDP provider of choice whether using OIDC and SAML (cloud and on-prem) or LDAP (customer managed)
The Members management tools allow organization admins to set access to individual products and then set more granular control within each product themselves. This enables multiple product admins to be able to work across the portfolio. Your Cribl Stream team can have its own admin that is separate from your Cribl Edge or Cribl Search admins. This allows your organization to scale without needing a single, monolithic admin to be the bottleneck for all access requests.
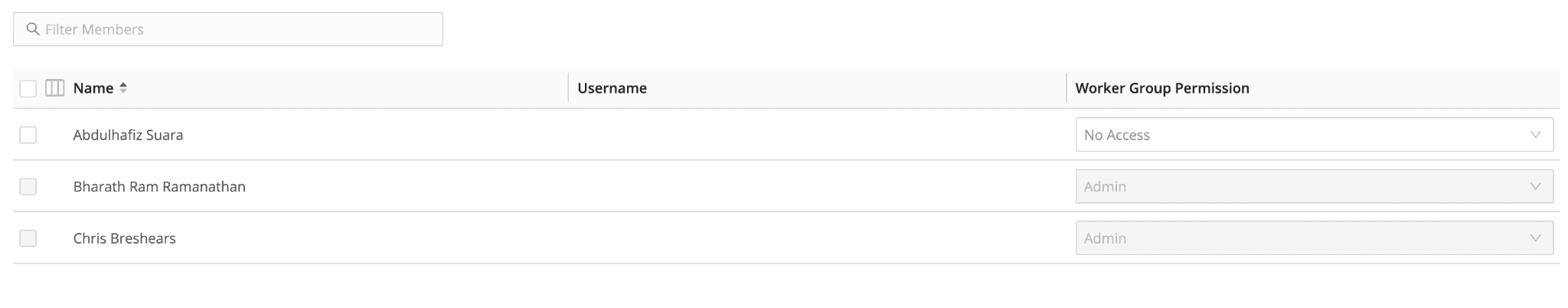
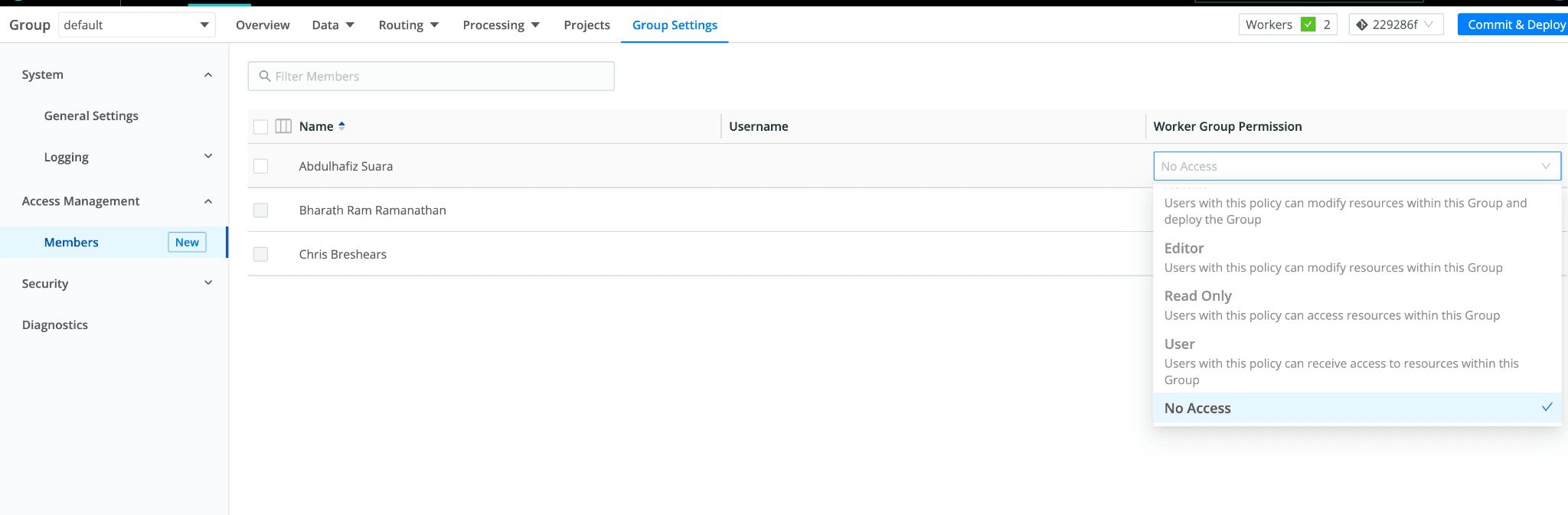
Below the Organization and product level, there are more controls to restrict access and capabilities to specific worker groups and fleets, and sub-fleets. We’ve taken an approach to provide customers with the most flexibility to manage their authorization rules. In its simplest form, a user can be granted Admin or Editor All capabilities across one or more products but we’ve also implemented the ability to ensure that a single Member can be restricted to a specific worker group or fleet/sub-fleet with additional levels of control. This enables organizations to not just control access to specific products but also manage users’ access to specific flows of data or collection of Edge agents.
But we can do you one better than that. With 4.2.0 we are introducing a new “share” concept in our products which will unlock granular controls of products at the resource level. For Stream this will show up the ability to share a Project with Stream Group Users, giving them an isolated project space where they can work with only the data made available to them. More about this is below. For Cribl Search, Admins and Editors can create and share dataset providers and lock users down to only use those providers that have been shared with them. This guarantees that users don’t have access to datasets that are outside of their permissions. This is in effect the ability to control access at the most granular level in Search.
We will be opening up more resources over time: Stream and Edge sources, destinations, routes, pipelines, and packs as well as tools for making sharing in bulk and across large teams even easier. With the new Org and product role model + the sharing model, we are empowering teams to create access controls at the level that meets their security needs.
With Cribl’s new authorization support, you can enjoy peace of mind knowing your organization is enforcing security best practices, improving compliance, and protecting data privacy by restricting a user’s access to the least required permissions to perform their job. This allows for better management on how data is being accessed, used, and stored, and prevents users from accessing data beyond what’s necessary for their job.
If you’re an admin, you’ll now enjoy easier, scalable authorization management and can better visualize, assign, and manage users and roles. This significantly cuts down on administrative burden and potential for error.
Security and Control Across Cribl Products
Let’s take a quick dive into how Cribl’s new authorization feature spans all three products:
Cribl Stream – Stream Projects
The increasing demand for Stream is a testament to its effectiveness in improving operations and enhancing security measures. With the rise of ITOps, SecOps, SRE, DevOps, and other teams embracing Cribl Stream, we are thrilled to introduce Stream Projects, which enables the secure expansion of Stream usage to more users within organizations. Here’s how Cribl’s authorization system facilities this secure self-service expansion of Cribl access to these teams.
Projects serve as shared resources and can be created by admins. Group admins have full control over projects in their assigned groups and can share them individually or in bulk with other users. Users can create pipelines and share them with fellow project users, granting different levels of access, such as read-only or edit. Product admins have maintain capabilities for all sub-resources.
Cribl Edge – Fleets and Sub-Fleets
Cribl Admins now have the ability to control access to specific fleets on a per-user basis. This feature is useful in organizations where certain individuals, such as SREs, have ownership of particular parts of customers’ cloud environments but should not have access to or control over fleets for data centers, or vice versa.
Similarly, there may be situations where Kubernetes teams prefer self-management and require restricted access limited to Kubernetes fleets only. In such cases, Edge Admins can restrict access to specific fleets based on user roles.
With Cribl’s new authorization feature, users can be granted access to specific fleets, and permissions can be configured for individuals within each fleet. Access is limited to the fleet itself and its sub-fleets, following the same permission inheritance principle as other Fleet Management features. Fleet users will only see the fleets they have been granted access to and can create sub-fleets within those fleets. On the other hand, Edge Admins have the ability to view all available fleets, create new fleets, and share them with users, granting them Read, Edit, or Maintain access.
Search – Datasets and Providers
Administrators need the ability to control who has access to data, not only to meet corporate security policies but also for efficiency, allowing more users to access the Search but with a limited range of access. They need the ability to define users and group policies to ensure that specific users or sets of users only have access to those specific datasets required for their roles. This release allows administrators to limit who may access/query which datasets, and defined sets of data (S3 bucket, Azure Object, Okta API, etc.).
This is just the beginning. Pipelines, routes, and dashboards are coming your way. Stay tuned for more updates as we continue to deliver more authorization support across all products. 🎉
Get Started with Cribl.Cloud — 1TB/Day for Free!
We’re seeing more folks wanting to try Cribl products in the cloud, and hearing more of our existing customers ask us to help them migrate their existing on-prem deployment to the cloud. And it’s no secret why. Cribl.Cloud offers:
Fast and easy onboarding. With zero-touch deployment, you can quickly start using Cribl products without the hassle, burden, and cost of managing infrastructure.
Instant scalability. The cloud provides flexibility to easily scale up or down to meet changing business needs and dynamic data demands.
Trusted security. The biggest hesitation we hear about working in the cloud is security. Cribl.Cloud is SOC 2 compliant, ensuring all your data is protected and secure.
Cribl.Cloud is the fastest and easiest way to start using Cribl products today. Get started with a free Cribl.Cloud account and use up to 1TB/day at no cost. Nothing to install, no infrastructure to manage, no license required, and no payment collected. You can also access Cribl.Cloud through the AWS Marketplace, Stream on friends!