Solutions Overview
Solutions for modern telemetry challenges
Explore how you can solve complex observability and security data problems — from reducing costs and modernizing architectures to optimizing your platforms and your industry.
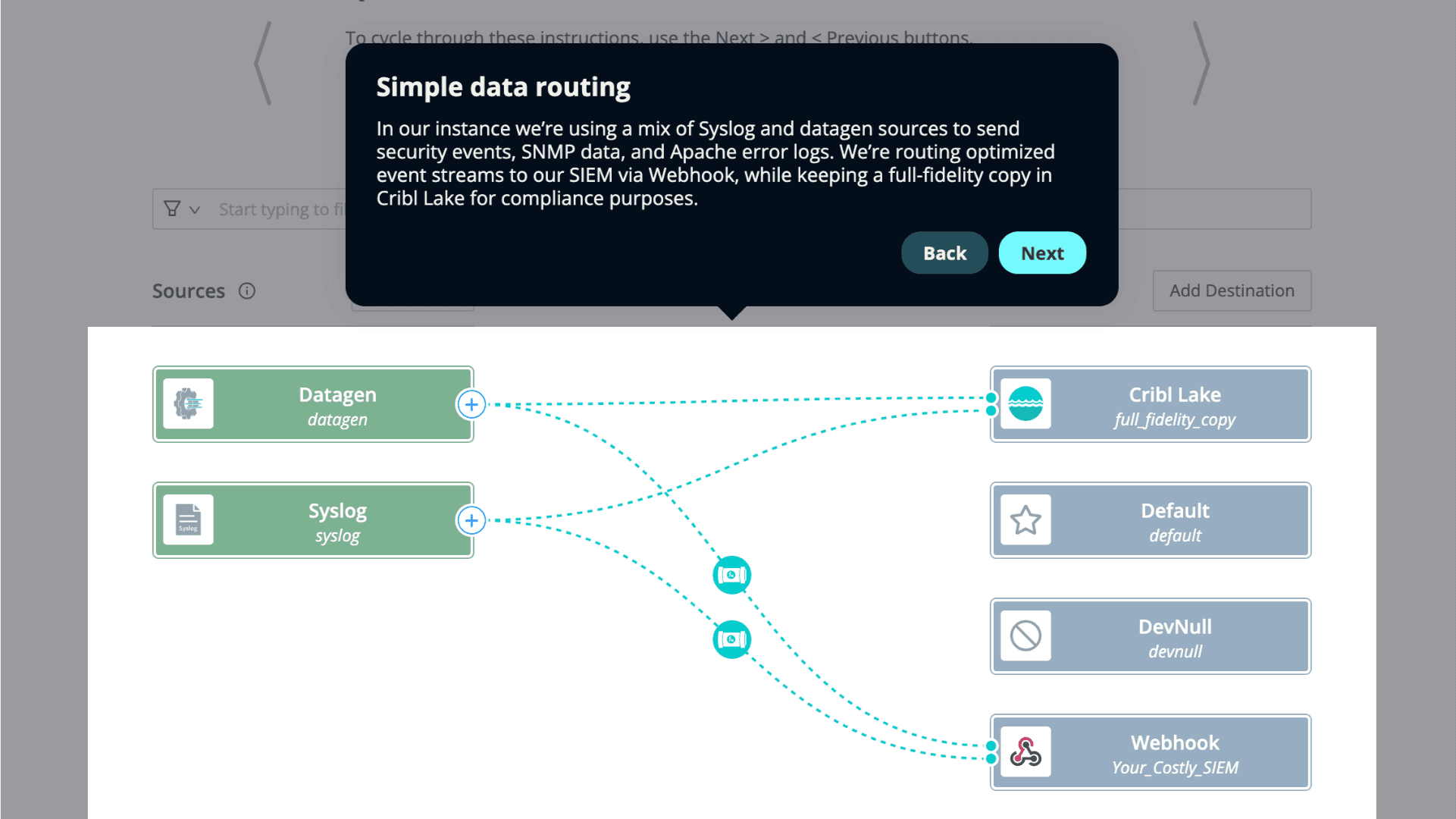
Explore how Cribl helps your team collect, transform, route, and enrich telemetry — to reduce cost, accelerate cloud migration, and make data actionable across IT and security operations.
From cost-control strategies to cloud and SIEM migrations, Cribl gives you expert direction to tame data sprawl, enhance observability, and unlock long-term operational and business value for your most important initiatives.
If you already use leading observability and security platforms, you’re in good company. Cribl integrates directly with them — helping you optimize telemetry, reduce costs, and get more value from the tools you already trust.
Optimize production, cut costs, or fuel innovation. Cribl helps your enterprise harness telemetry data for operational clarity, faster decisions, and measurable outcomes — no matter where you work.
Demo

get started
See demos by use case, by yourself or with one of our team.
Get hands-on with a Sandbox or guided Cloud Trial.
Process up to 1TB/day, no license required.