It wasn’t that long ago that some coworkers were excited to use GraphQL as an alternative to REST APIs. Then recently, the topic of gRPC came up. An actual RPC over HTTP is a powerful concept. It uses Protobuf.
Previous experience with Protobuf was just painful, to be honest. How complicated is this? Worth doing? All of which caused me to think about how to analyze gRPC. Since AppScope extracts payloads from network activity, could we see gRPC and Protobuf details?
I set about building and running the obligatory Go gRPC helloworld. The Quick Start on grpc.io is nice. Accurate and works well. I “scoped” the server, and started getting events and payloads. Quick and easy:
$ scope run -p — go run greeter_server/main.go
Now that I could capture all of the traffic between the gRPC server and any client, I needed to determine how to analyze this binary data. Wireshark, of course, is the tool to use – it has a ton of protocol support, including gRPC. So I checked out Analyzing gRPC Messages Using Wireshark on grpc.io. Another nice description. However, you quickly run into the following:
Currently, Wireshark can only parse plain text gRPC messages. While Wireshark supports TLS dissection, it requires per-session secret keys.
That’s disappointing, because the Go implementation of gRPC uses HTTP2, which, of course, implies HTTPS and encryption.
Fortunately, AppScope emits payload data before it’s encrypted and after it’s decrypted. This means that data can be fed to Wireshark without dealing with session keys. This is a two-step process:
Step 1: Convert the binary data to a pcap for Wireshark.
Use hexdump on the binary, then convert that to a pcap – this works well.
$ hd -v ~/.scope/history/go_13_3798_1616170558341724813/payloads/3896_\:\:ffff\:127.0.0.1\:59944_\:\:ffff\:127.0.0.1\:50051.in > grpcres.hd
$ text2pcap -4 127.0.0.1,127.0.0.1 -T 50051,59914 grpcres.hd grpcres.pcap
Step 2: Open the pcap in Wireshark.
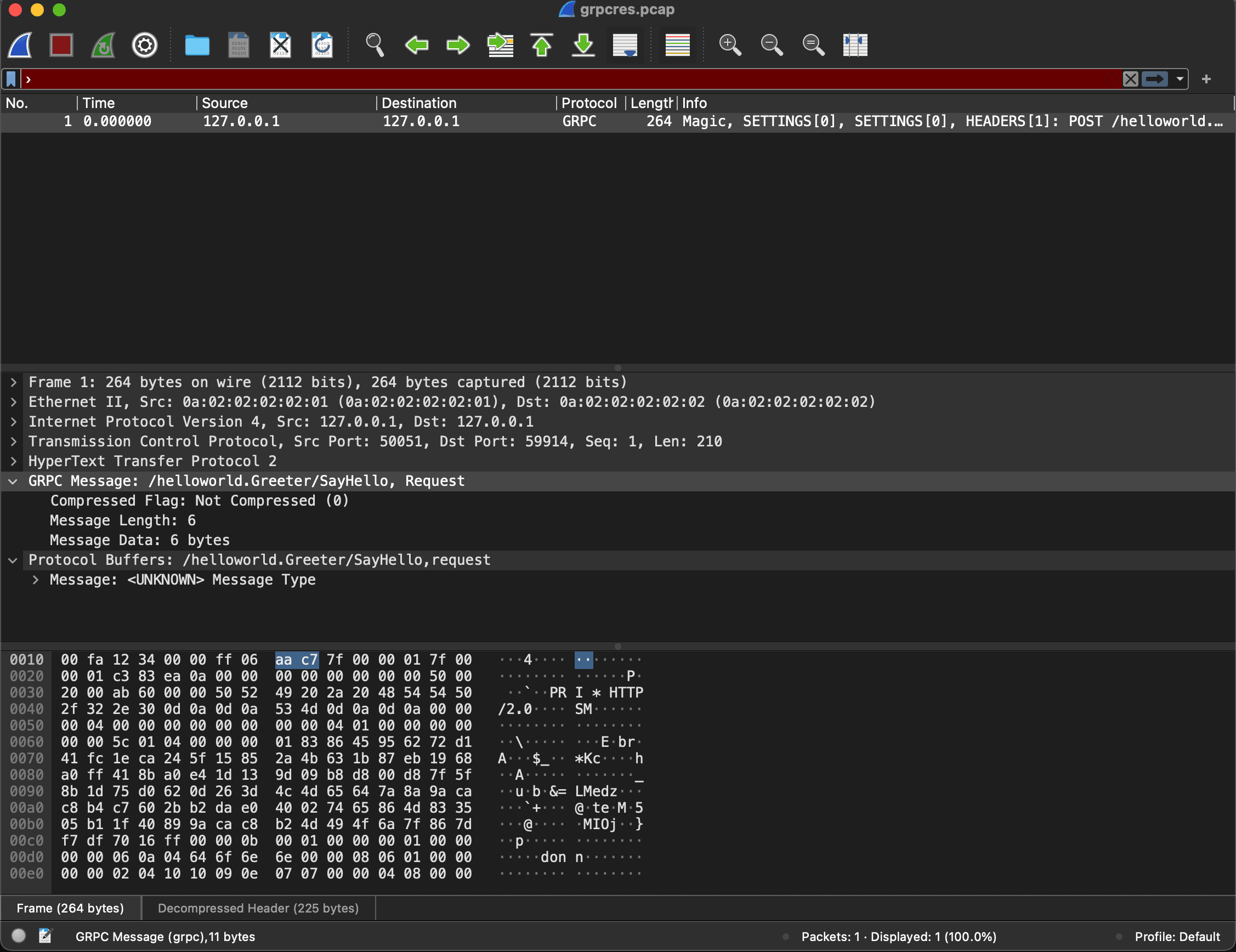
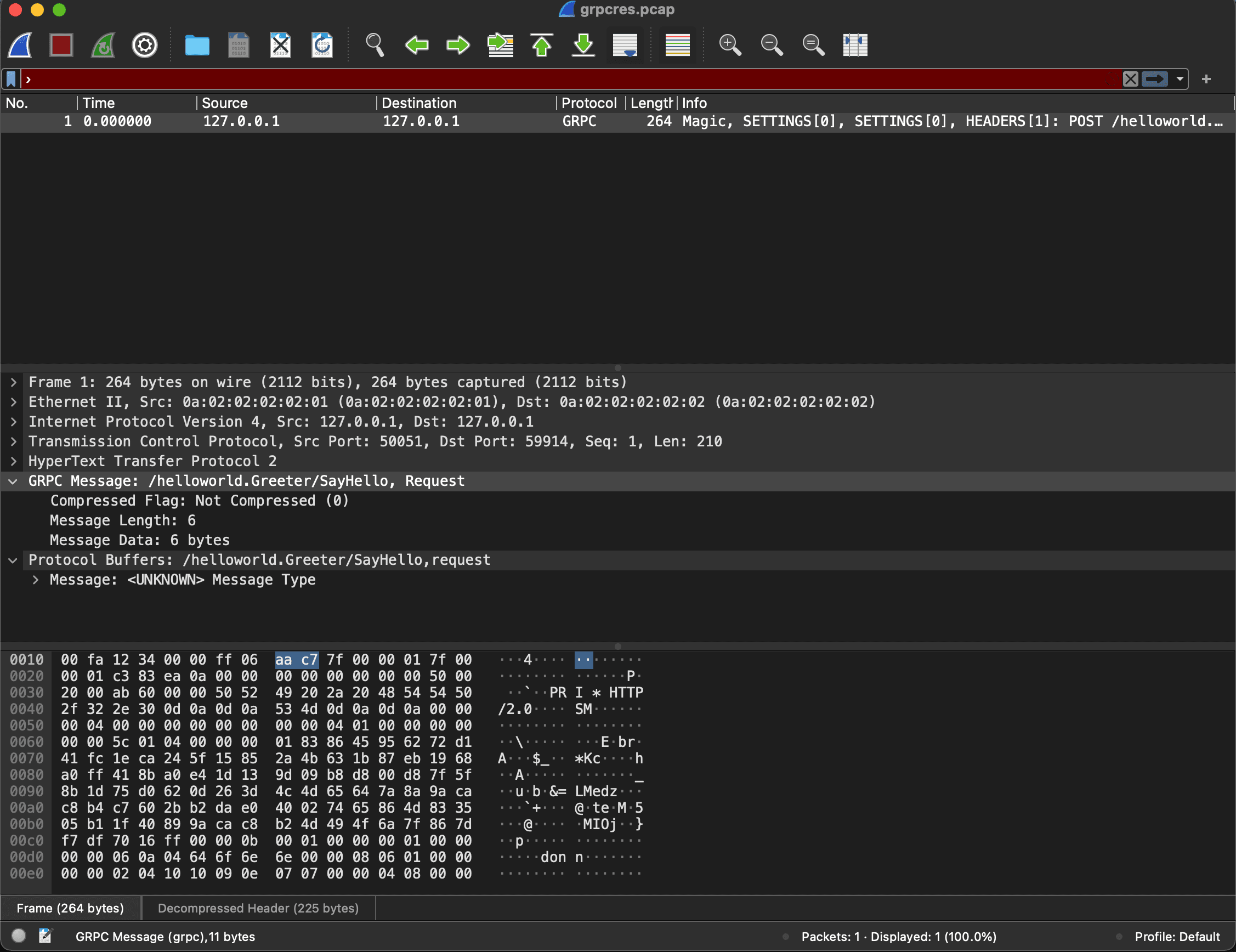
In the server response, we see details of the gRPC response and the related Protobuf. (To see and parse details of the Protobuf content, I pointed Wireshark to the proto file for this app: Wireshark Preferences->Protocols->ProtoBuf->Protobuf search paths.)
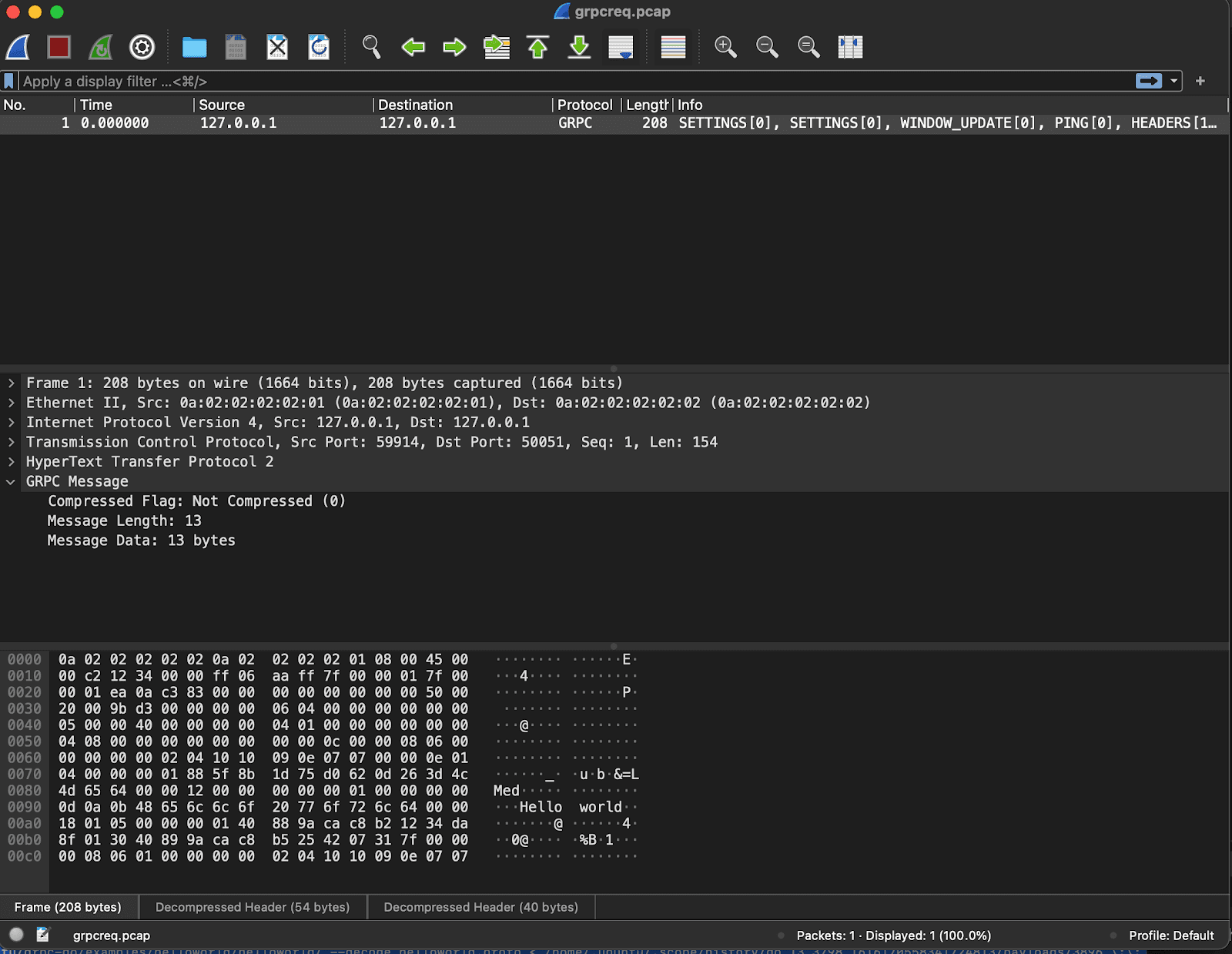
The request sent to the server is pretty straightforward. We see the specific function call on the remote server, which is the salient point.
We’ve demonstrated that AppScope can analyze gRPC protocol traffic, including traffic that is encrypted. The steps include using AppScope to extract payloads from a gRPC client or server, converting the payload data to a pcap format, and using Wireshark to analyze protocol details.
To learn more about AppScope, visit the website and try our AppScope Fundamentals Sandbox course.