In this live stream, Sidd Shah and I discuss how Cribl Stream can empower Security Operations Admins to make the most of their CrowdStrike FDR data. They address the challenges faced by CrowdStrike customers, who generate a vast amount of valuable data each day but struggle to leverage it fully due to complexity and size. They also explain how Cribl Stream can help SecOps admins extract the right data for their SIEM while moving the rest to their security data lake, enabling them to get the maximum value from their data and be cost-effective at the same time.
The post below is an excerpt from this conversation — highlighting a case study where Sidd was able to help a customer reduce their CrowdStrike FDR data from 1TB per day down to 250GB.
What Is Crowdstrike FDR Data?
CrowdStrike FDR collects all sorts of near real-time data about your environment, including asset and identity detections. The data is very high quality, but the amount it collects is non-trivial, and customers typically are not prepared or equipped to get value from it — we’ve seen such high amounts that it would have doubled some customers’ SIEM licenses.
In these large quantities, you simply can’t afford to send all the data through your systems of analysis, and it’s tough to get full value from a tool like this if you can’t utilize the data it generates. Part of the reason for the quantity issue is that CrowdStrike data is redundant — this isn’t unique to them necessarily, but if you take a close look, you’ll find that CrowdStrike even creates logs about the data it’s sending to itself!
The Benefits of the Trend Toward Data Lakes
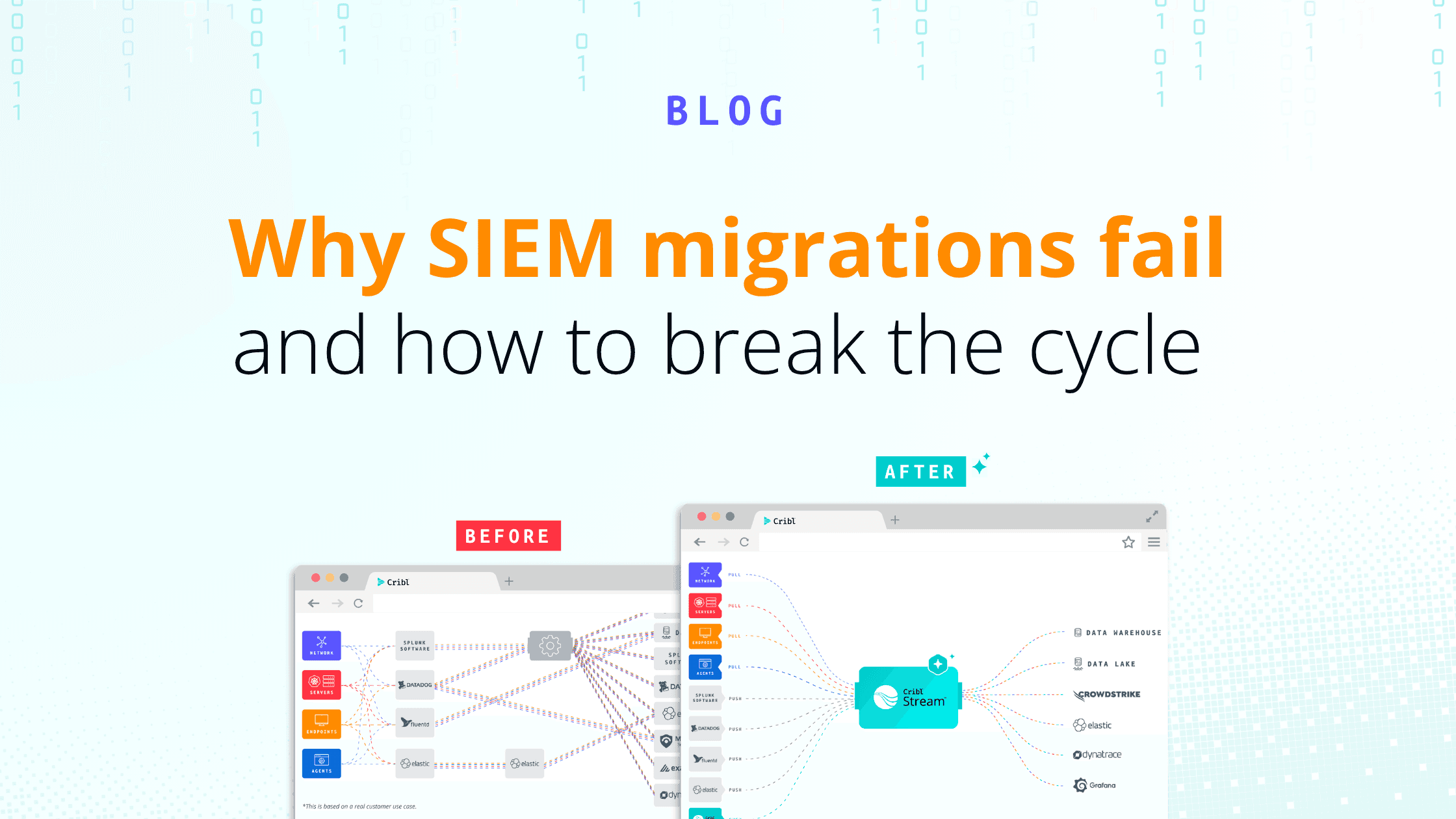
One of the trends we’re starting to see, especially in the security community, is the idea of sending only what’s necessary for detection and response to the SIEM and sending everything else to a security data lake or object storage like an S3 bucket. This way, enterprises can get better, cheaper analytics options and still meet compliance and regulatory requirements, all while keeping control of their data.
Being able to send a copy of data to an object store lets you manage your retention in a world where data growth is far outpacing the budgets available to manage it and allows you to decouple your retention requirements from your SIEM. Then, you can use Stream if you ever have to bring that data back, or you can use Cribl Search to query that data in place on an as-needed basis.
Using Cribl Packs to Get a Jump Start on Configuration
To get started handling the quantities of data the CrowdStrike and other tools are sending your way, Cribl offers a series of packs available in our Cribl Packs Dispensary. The packs are a set of configurations that match a use case — the CrowdStrike-specific pack helps users look at common data sources or data types that come in via CrowdStrike FDR and gives some of the best practices around parsing, filtering, reducing, or aggregating this data.
We configured this integration with network security data admins in mind, removing as many pain points associated with onboarding new tools as possible. When we showed a recent customer how to set CrowdStrike up as a source in Stream, it took about 15 minutes as opposed to the hour they were expecting it to take — everyone on that call got a nice bonus of 45 minutes of their day back.
After we set this up, our customer turned CrowdStrike FDR back on and got about 1TB per day of data as opposed to the 60GB they were expecting. This would have completely eaten up their SIEM license if it continued, so we used Stream to figure out what event types were there, turned them into metrics, and sent them to their metrics store. That way, as we worked through it every day, we could go back to that metric storage and see which data sources were the largest and tackle those first.
After that, we worked with them to demonstrate how to turn each of the dials up and down on their own because they need to be able to calibrate things to create the right balance between filtering out unneeded data and still getting value from what’s left. In the end, they were able to reduce the 1TB per day they were ingesting to about 250GB per day, and still come in under their SIEM license.
Not only that, but they made the data they decided to keep even more valuable by moving on to enrichment with Redis, DNS data, and timestamping. Their new configuration will also make it easier to do threat hunting in the future, because of the huge increase in the ratio of signal to noise and the ease with which they’ll be able to search data in their data lake instead of their SIEM.
Watch the entire live stream on Getting the Most Value from CrowdStrike FDR Data with Cribl Stream to see how you are able to make all these changes and watch how the data is being transformed in real-time, without any trial and error or finger crossing and hoping for the best. If you’re a SecOps admin looking to make the most of your data — this video is for you.