This technical content is no longer valid (2024-03-14).
Video conferencing usage, especially on Zoom, has exploded in the last few months, and companies small and large are using it extensively to enable and connect their now mostly-remote employees. And, as with any other critical technology, especially when interconnecting infrastructure, it’s important that administrators get real-time visibility and insights into it, such as:
Average length of meetings over time
Meeting counts/frequency over time
Number of participants per meeting
Meetings that end on time, over time etc.
Webinars user registrations, Recording stats, etc.
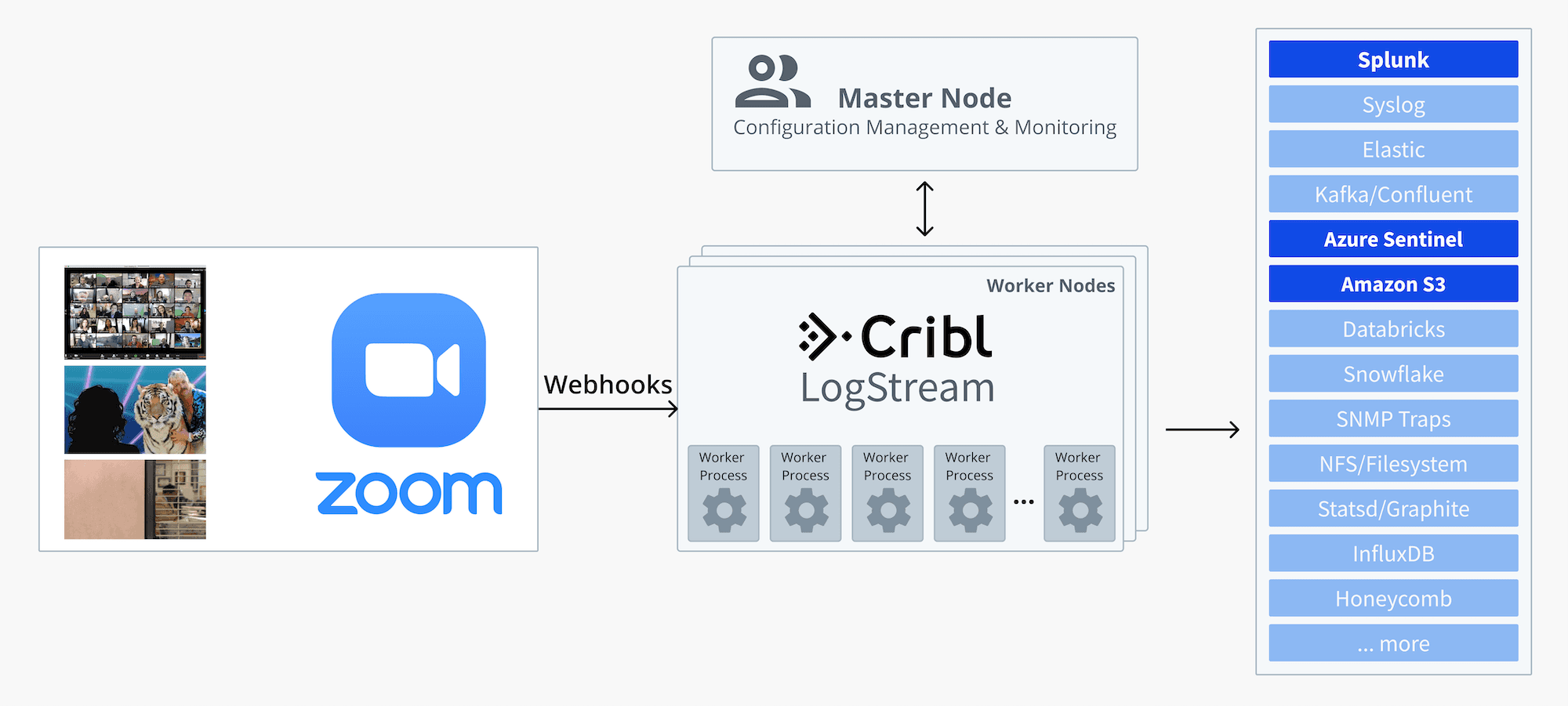
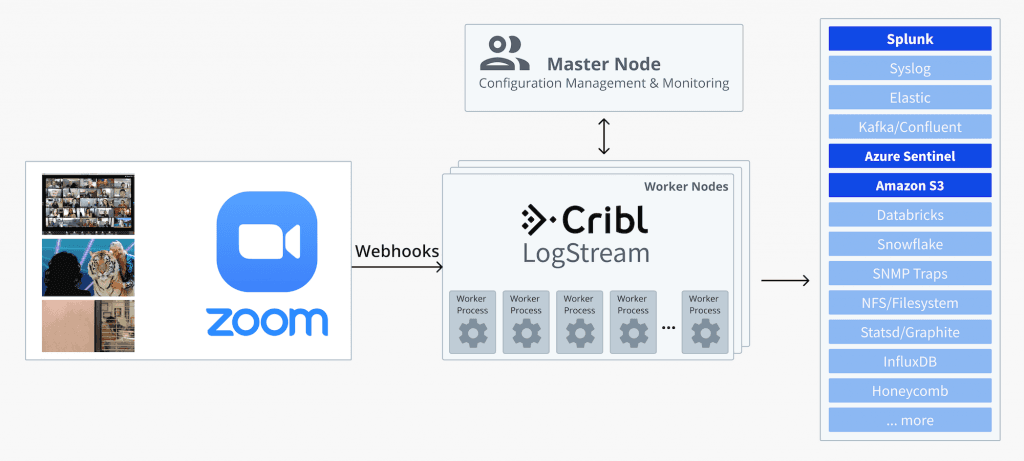
In this blog post, we’ll explore integrating Zoom log data into Cribl LogStream and route it to a destination of choice. For instance:
Send a copy of the data to Splunk for operations teams (here you can choose to anonymize usernames or other sensitive information),
Send a second copy to Microsoft Sentinel for use by the security team,
Send a third copy to Amazon S3 for long-term archiving.
1. Set up LogStream to receive Zoom data
Zoom can be configured to send account activity logs out via Webhooks. On the LogStream side, we can receive those calls via our native HTTPS Source. To set this up, go to Data > Sources and select HTTPS. Assign this Source a name and provide a port number, e.g., 7003. Make sure that this port is reachable externally, or at a minimum, from Zoom’s IP addresses.

Leave the Auth Token field here empty for now, or enter a fictional one – we’ll come back and edit it after we complete Step 2.
Next, enable TLS, and provide your key and certs as necessary. If you don’t have a cert/key, then you can create and use a self-signed one. E.g.:
openssl req -nodes -new -x509 -newkey rsa:2048 -keyout myKey.pem -out myCert.pem -days 420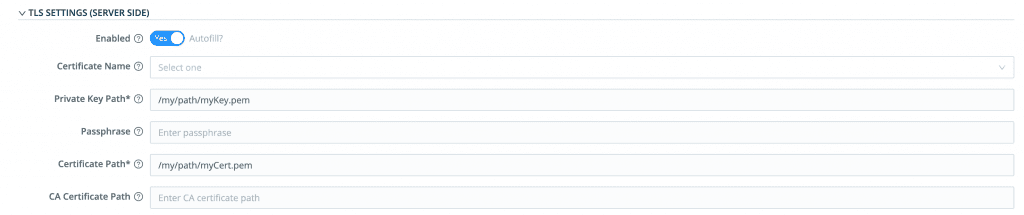
2. Set up Zoom to send data to LogStream
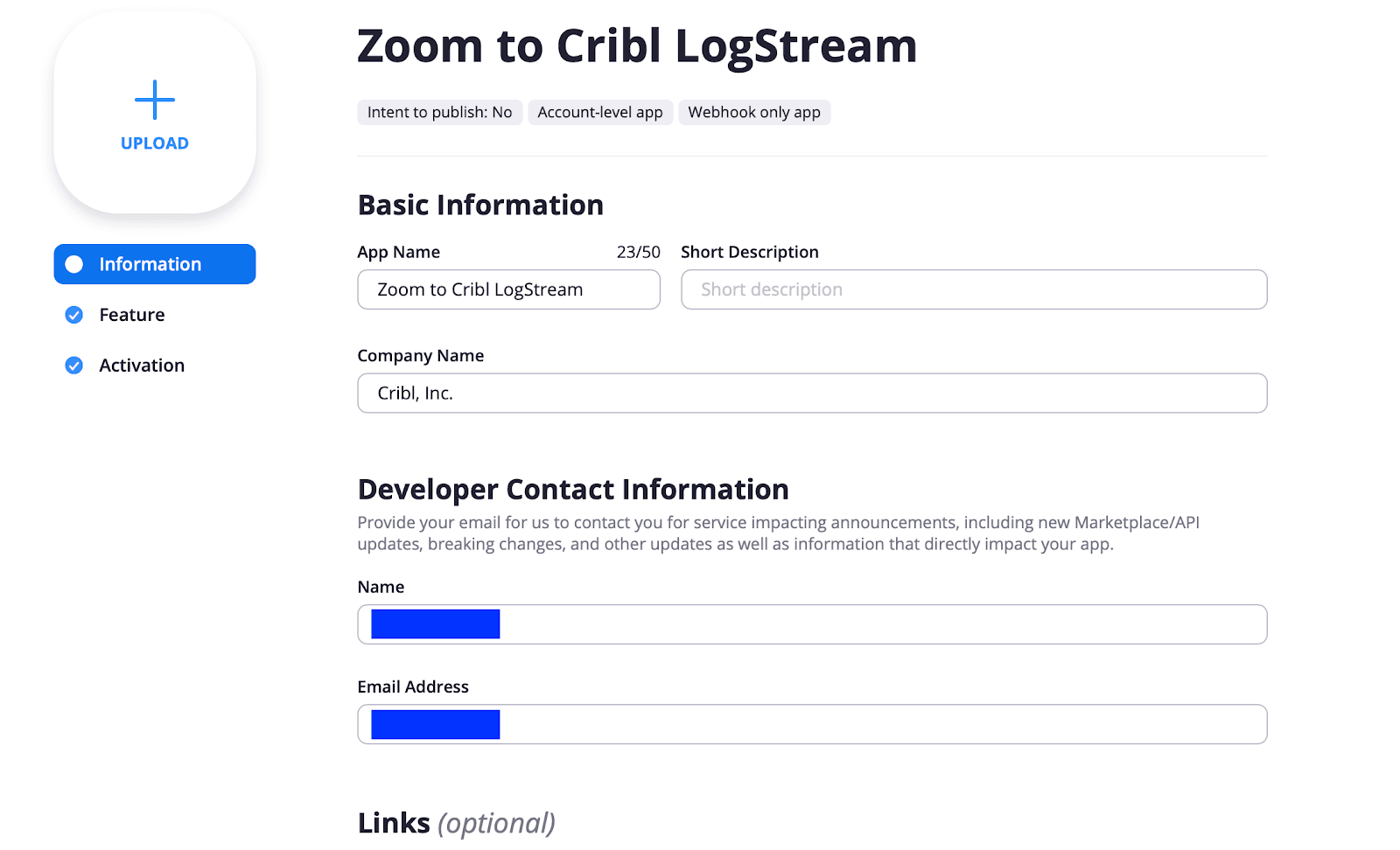
To set up Zoom to send data, go to marketplace.zoom.us and log in to your account. Find Develop at the upper right and click Build App.

Next, select Webhook Only and click Create.

Name your app. Then fill in the Basic Information and Developer Contact Information required on the next form, and click Continue.
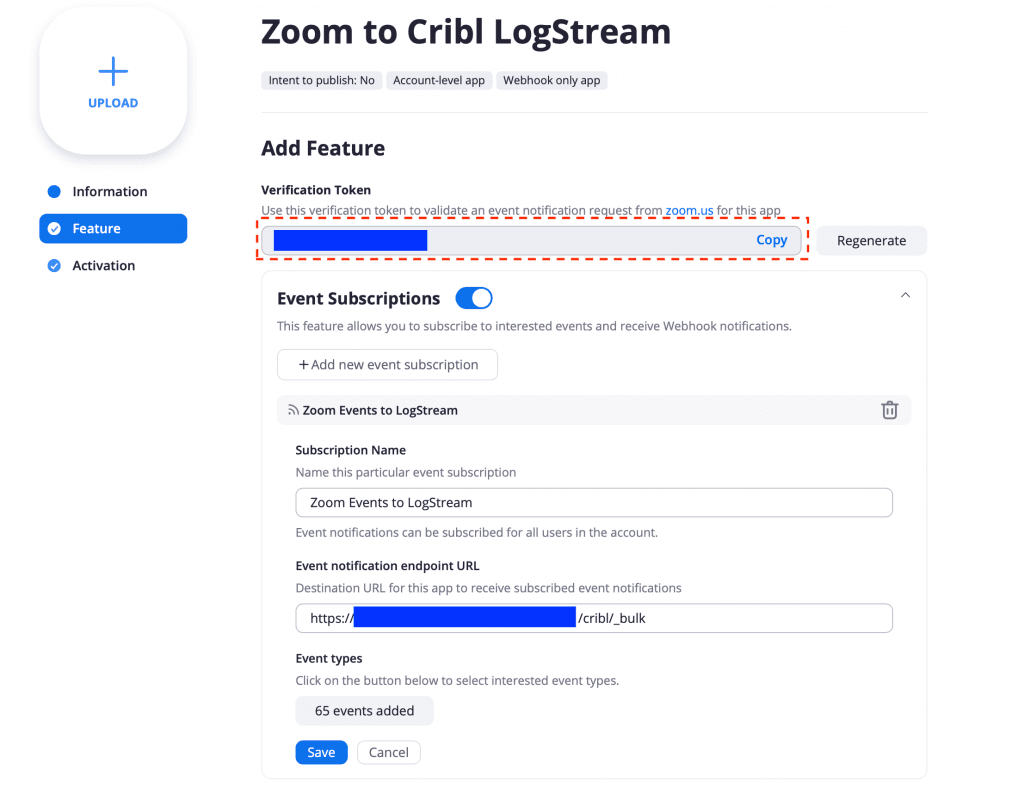
Next, on the Add Feature page, enable Event Subscriptions and a new subscription – in our example, we’re calling it Zoom Events to LogStream. In the Event notification endpoint URL, enter the destination URL that Zoom will send events to. This is the LogStream HTTPS Source address from above, in https://<logstream-hostname-or-ip>:7003/cribl/_bulk form. Next, click the Add events button and subscribe to your desired Webhook Events. In our case, we subscribed to all. Then click Save.
Finally, click Activation to activate the Webhook Only App.
Navigate into the Feature tab, copy the Verification Token string, and use this to update the LogStream HTTPS Source we created above. This token verifies that the event notifications that you receive are originating from Zoom.
We should now be connected. To capture live data in LogStream, navigate to our Source, click on the Live button, and then on Live Data. If there is current Zoom activity, the capture should show something like this:

3. Set up LogStream to route Zoom data to your destination
Now that data is flowing in, we can create an Output Router that sends this data to three destinations. Output Routers are found under Data > Destinations, and they allow for output selection based on rules. Rules are evaluated in order, top‑>down, with the first match being the winner.
To clone data, all we need to do is set the Final flag to No. For example, the Output Router below, called zoomRouter, is configured to forward all incoming data to three outputs: a Splunk Destination called localSplunk, an Azure Logs Destination called sentinel-monitor-logs, and finally to an Amazon S3 Destination called zoomLogs. (Each of these Destinations is configured individually, and here they’re just referenced.)

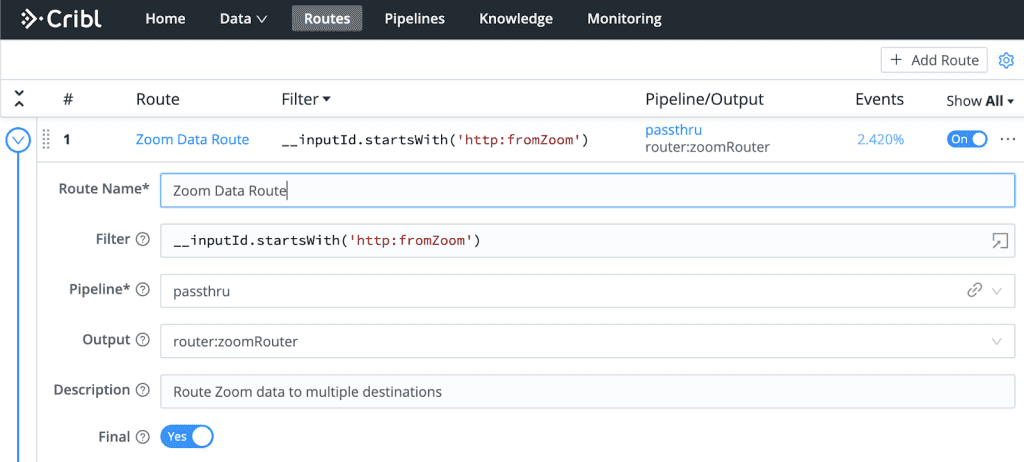
To engage the Output Router, we create a Route called Zoom Data Route that targets specifically our Zoom data, using a Filter on the Source we created above:
__inputId.startsWith('http:fromZoom')Since we don’t need any processing, we use a passthru Pipeline. And as an Output, we select the Output Router we just created above.
That’s it – done!
With a wide support for a large number of Sources and protocols, LogStream enables you to receive your video conferencing logs and forward them to your security and operational analytical stores reliably, at scale, and without any custom code.
—
New to Cribl LogStream? Take our Sandbox for a drive!
If you have any questions or feedback, join our community Slack – we’d love to help you out. If you’re looking to join a fast-paced, innovative team, drop us a line at hello@cribl.io – we’re hiring!