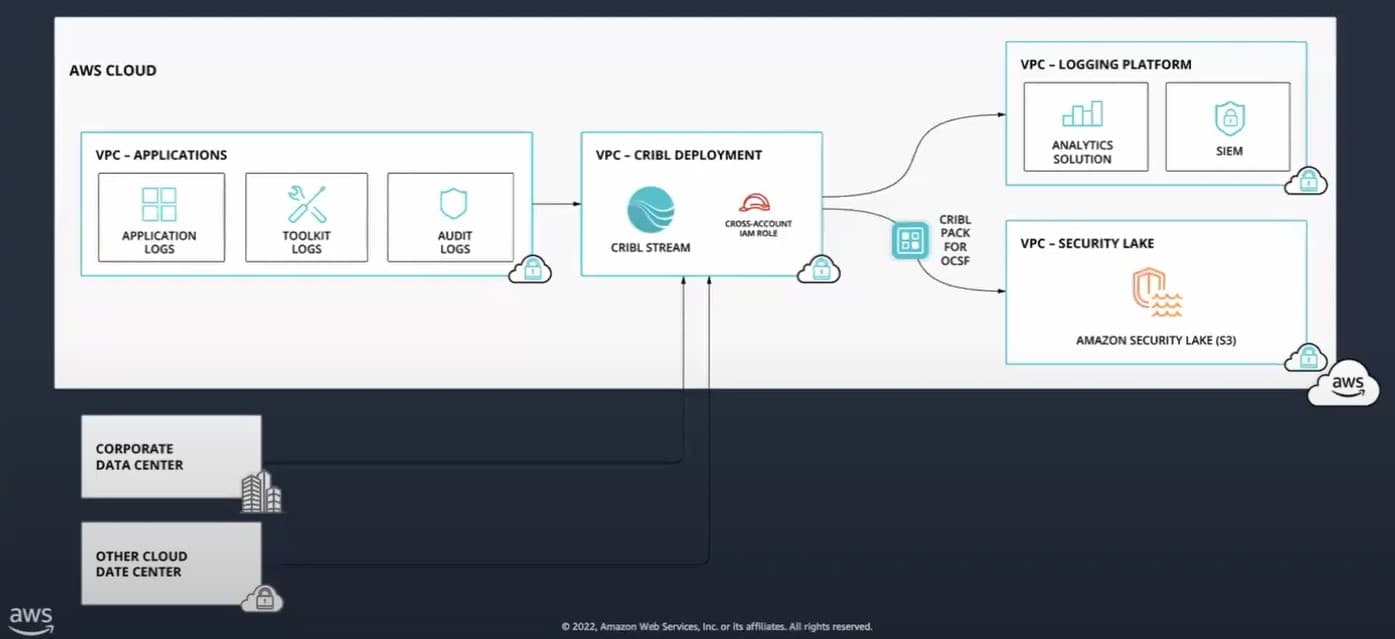
In a recent user group meeting, guest speaker Marc Luescher from Amazon Web Services (AWS) joined us to give an overview of Amazon Security Lake. We talked about Cribl use cases and how Cribl Stream can bring your non-AWS data into the Security Lake.
Enterprises are dealing with some significant challenges with security data in 2023. Inconsistent, incomplete, poorly-formatted log data is simultaneously scattered across companies and locked up in different silos within the organization.
As if that isn’t enough, security data is growing by about 30% per year, making managing it even more difficult. If your data is exactly where it needs to be, in the format you want it in, and you’re miraculously keeping up with this pace of growth, getting it to a place where you can analyze it requires specialized tools that end up creating duplicates and increasing licensing costs.
Another big problem is the lack of direct control over data, which often gets locked into a SIEM or another tool that makes it hard to get the data out again if needed.
To help address the issues, AWS, Splunk, and a few other organizations announced that the open cybersecurity schema framework (OCSF) would be public domain as of August 2022. OCSF is an open-source project designed to deliver simplified security data.
What Is a Security Lake?
All that simplified security data is stored in Amazon Security Lake — a centralized location for data from AWS environments, SaaS providers on-prem, and cloud sources across AWS regions. The Security Lake caches, pre-processes, and normalizes security data in the OCSF standard for more efficient storage and query performance — so you can use your vendor of choice to look at and control your data.
It also consolidates the data from VPC, CloudTrail, Route 53, S3, and Lambda — as well as event findings from the AWS Security Hub and connecting services like AWS GuardDuty, Inspector, IAM Access Analyzer, Macie, and more. The Security Lake is stored on an S3 bucket in a management account where you can query it using Amazon Athena, OpenSearch, SageMaker, or your SIEM/XDR tool of choice.
With the Amazon Security Lake, you can integrate data from over 60 sources, normalize AWS logs in OCSF, and store data in an S3 bucket. Security Lake centralizes security-related logs and findings, helping Security Operations teams streamline their process so they can spend more time investigating security issues and less time collecting and normalizing logs. The data lifecycle management capabilities allow you to specify data that’s old enough to be archived, so you don’t have to keep it in Glacier Flexible Retrieval instead of some other more expensive storage. You can still use your analytics tool of choice as long as the vendor supports OCSF.
Leverage Cribl Stream to Bring Non-AWS Data to Amazon Security Lake
Using Cribl Packs to Bring Non-AWS Sources Into Amazon Security Lake
Cribl Packs allow Cribl Stream customers to build and share configuration models across distributed Cribl Stream deployments. The pre-built pipelines, lookups, data samples, and knowledge objects reduce costs and engineering time by reducing complexity and giving users an isolated, secure space to build, test, and share their work. This enables your team to accelerate data onboarding from any 3rd party source to gain greater visibility across your security and operating environments
Packs are available in the Cribl Packs Dispensary to support bringing data from these sources into your Amazon Security Lake: CrowdStrike, Palo Alto threat and traffic logs, Azure audit logs, GCP audit logs, Zscaler web and firewall logs, Cisco ASA and FTD, and Sentinel One Cloud Funnel. Of course, we make it easy to convert your data into OCSF as you move data into Amazon Security Lake.
Build a Custom Cribl Pack to Convert Any Log Source to OCSF/Parquet
You also have the option to build your own pipeline and Cribl Pack to support the conversion of any log file to OCSF/Parquet format and get it to your Amazon Security Lake. This allows you to enrich raw data from any source with a repeatable transformation process that requires minimal effort for modifications.
Here is some information on how to create a Cribl Pack — stay tuned for more detailed instructions for making them compatible specifically with Amazon Security Lake.
Search Data In Security Lake Using Cribl Search
Using Cribl Search to search data in Amazon Security Lake is like having a superpower. In one of our previous blogs, we dove deep into the benefits of setting up a data loop with Cribl Search, Cribl Stream, and your own data lake. Using Cribl Search, you can increase the scope of analysis and mine data at rest in OCSF for quicker searches to capture deeper insights.
Ready To Get Started?
Learn how Cribl can help you with your AWS use case with a custom demo. Test it out for yourself by leveraging our AWS-validated open-source Cribl Packs and our Amazon Security Lake destination tile with a Free Trial of Cribl Stream on AWS Marketplace.